Remotely access Pi system stats
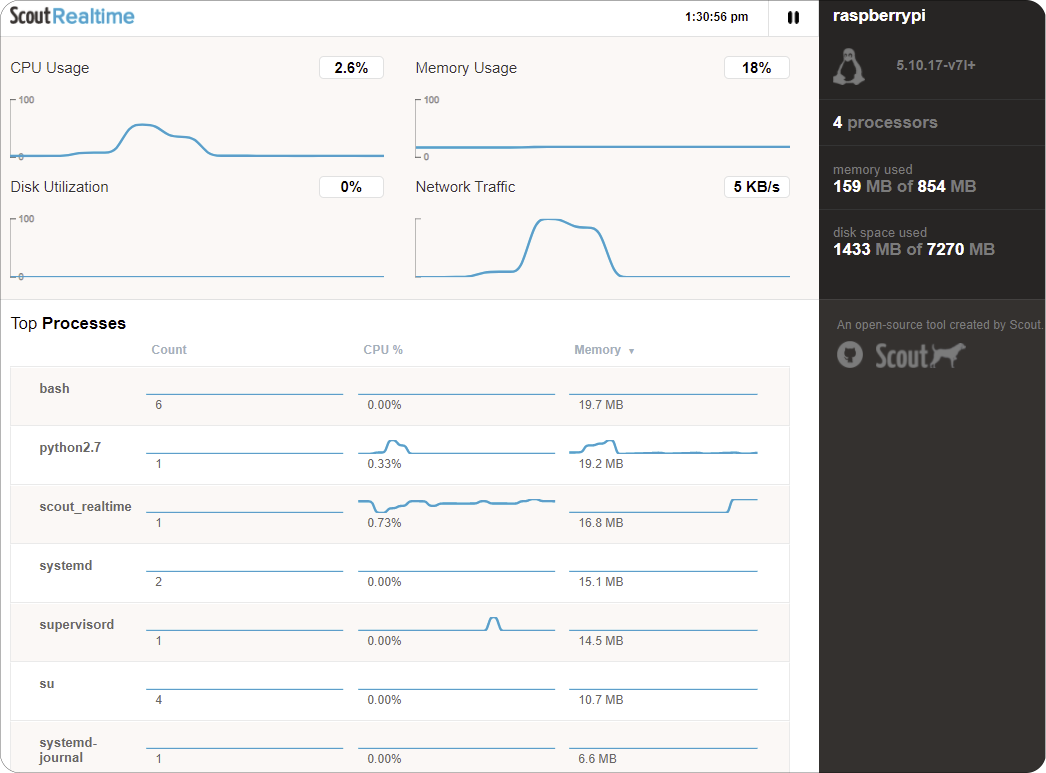
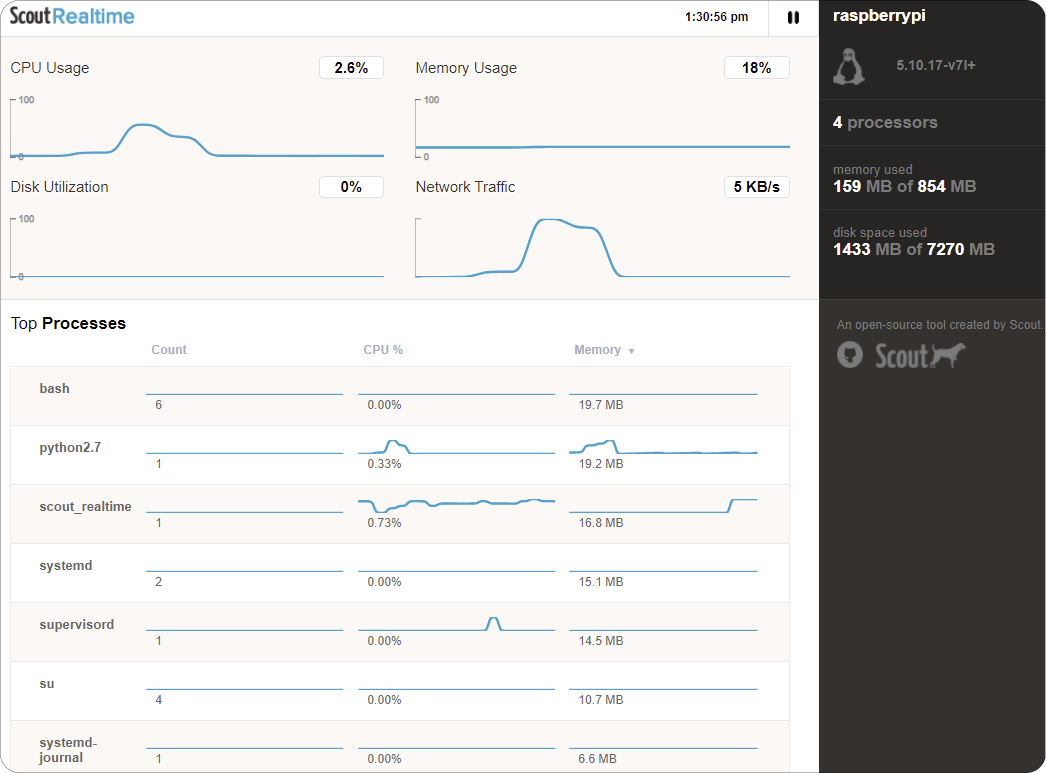
Use ScoutRealtime to remotely access a beautiful view of your Pi system stats
In this example we use Wormhole to remotely access critical system stats from a remote web browser. The system stats are available from anywhere, without port forwarding, as long as your Pi has internet access.
Overview
To see the system stats remotely we'll be installing ScoutRealtime - which is a nicer looking web version of HTOP.
Please ensure the following before proceeding:
- Pi is connected to the internet.
- Dataplicity is installed.
- We are logged in as Pi user.
- Port 80 is free.
Install ScoutRealtime
Scout is packaged as a Ruby "Gem", which means we first need to install the package containing the Ruby programming language.
sudo apt install -y rubyNext, install the scout_realtime gem.
sudo gem install scout_realtimeKudos to the ScoutRealtime guys! That's about as easy an installation as it gets.
Start the web service
At this point, Scout is installed and is ready to launch.
For Wormhole to work, when launching Scout we must instruct Scout to bind on HTTP port 80 instead of its default port.
sudo scout_realtime --port 80See your system stats remotely
Having completed the steps above we're now ready to use Wormhole to access the ScoutRealtime app. Normally, to access our wormhole we will find its link in our device's options pane:
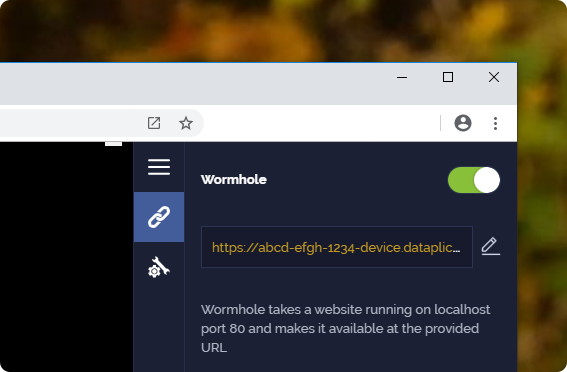
Using our wormhole link that will look similar to:
https://ABCD-EFGH-1234-device.dataplicity.io/Where the ABCD-EFGH-1234 part will be unique to our account. We enter this link in our browser and we will be presented with the view of the system stats.
Security considerationsDon't forget that when you switch on Wormhole you're placing the web service hosted on your Pi directly on the wider internet. That's actually the point, but what it means is that you need to take special care over what you put online.
In this case ScoutRealtime opens port 80 on your Pi and does not by default require a password to view. Wormhole listens only on localhost, and as such it is not necessary to open these ports directly from your Pi to the wider world. Therefore we recommend that you close these ports. If your system stats constitute private information it would be advisable to place the webserver behind NGINX and enable HTTP authentication (i.e. a password).
We've put together some basic tips for Securing Wormhole - well worth a read.
Updated about 1 year ago
